![An improved primer set and amplification protocol with increased specificity and sensitivity targeting the Symbiodinium ITS2 region [PeerJ] An improved primer set and amplification protocol with increased specificity and sensitivity targeting the Symbiodinium ITS2 region [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2018/4816/1/fig-2-full.png)
An improved primer set and amplification protocol with increased specificity and sensitivity targeting the Symbiodinium ITS2 region [PeerJ]

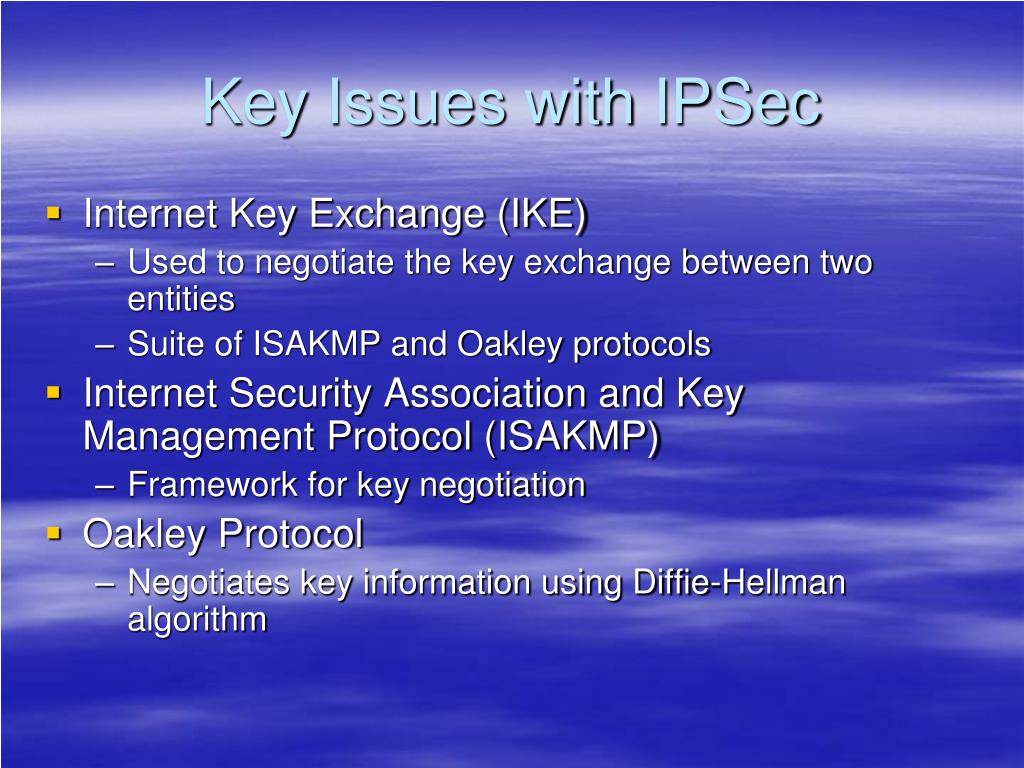
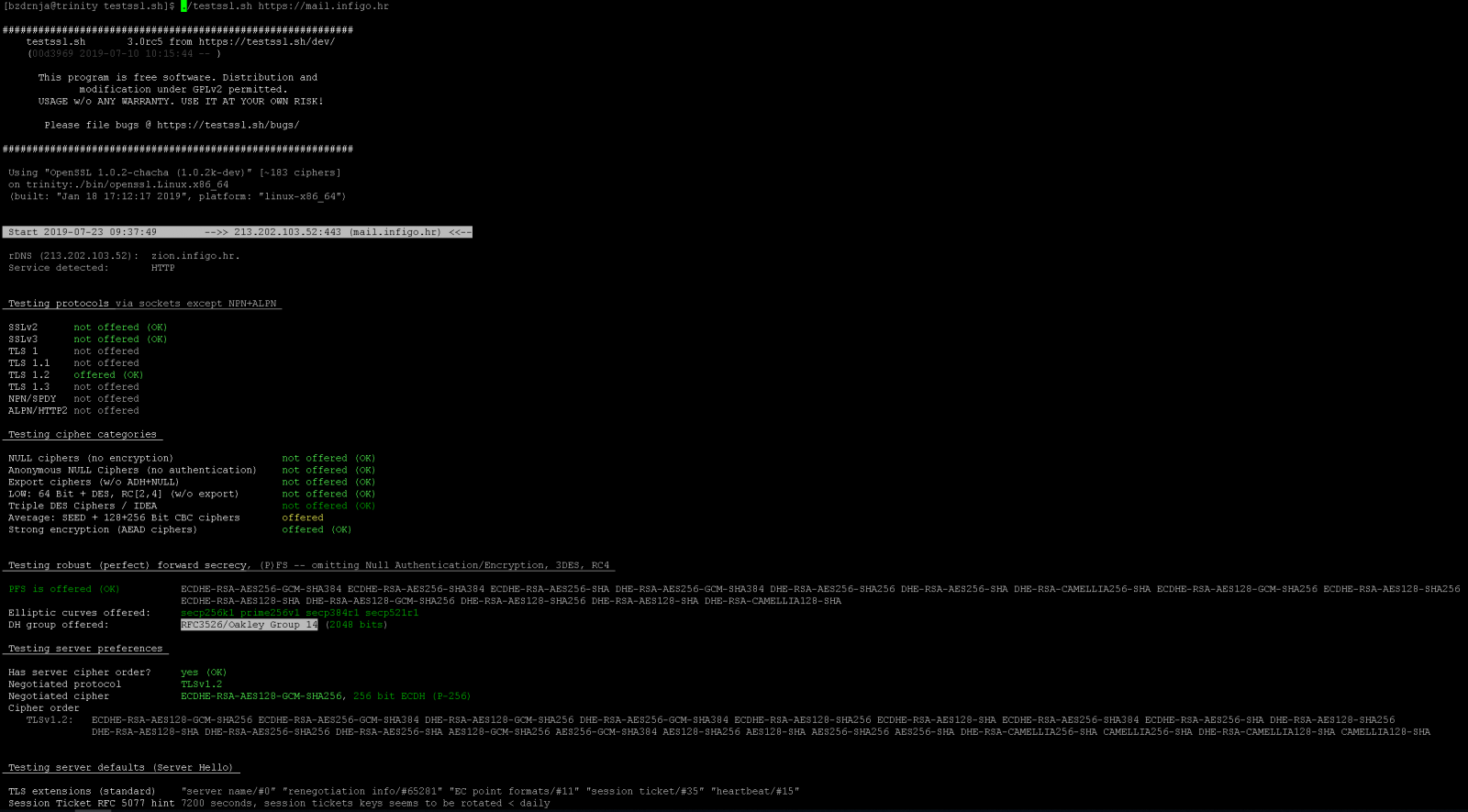
Implementing and Testing IPsec: NIST's Contributions and Future Developments Sheila Frankel Systems and Network Security Group NIST - ppt download

Amazon.com: OhO Bluetooth Sunglasses,Open Ear Audio Sunglasses Speaker to Listen Music and Make Phone Calls,Water Resistance and Full UV Lens Protection for Outdoor Sports and Compatiable for All Smart Phones : Electronics

Computer Security and PGP: What Is Diffie - Hellman Key Exchange Protocol or Oakley Protocol? | Computer security, Security, Secret